The Architecture¶
An example of a configuration for the ft6 is shown in the following picture.
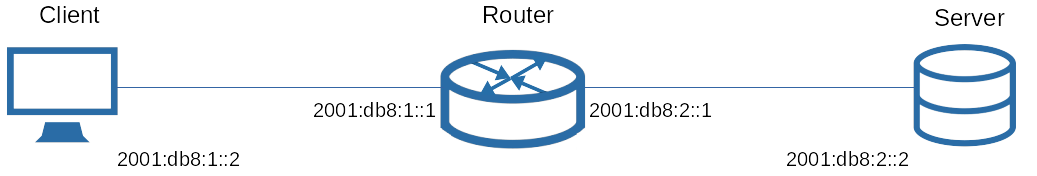
ft6 is a client-server application. The client (here with address 2001:db8:1::2) will send data over the network (via the router with the two interfaces as shown above),
which the server (2001:db8:2::2) attempts to capture. The server will then send back to the client a list of messages it received.
That way, the client will know what messages were blocked (or lost) along the way.
Note the word “lost” in the parentheses above. Client and server will not be able to figure out why a message wasn’t received at the server.
They will, however, always assume that a packet was lost due to the firewall blocking it.
To make the results meaningful you must make sure to not accidentally test some other devices as well.
When setting up, it is therefore important to place the client and server directly one hop away from your firewall, to ensure that no other devices are interfering with the traffic.
Most communication will be sent via UDP with the destination port defaulting to 80 (www).
That means you need to provide at least one open port for ft6 to work.
Also, if your firewall policies are very different for each service you provide, it might be useful to check each port separately.
ft6 marks packets with strings like "XXXXXXTest1Step1". If your firewall rules match such strings ft6 will likely fail.
Client and server also perform a kind of handshake, by sending messages:
- "
StartTestn" - "
EndTestn" - "
StartResultn" - "
EndResultn" - "
ACKNOWLEDGED"
(with n being and integer). Please don’t block those either.
Continue Reading at Running ft6 or go back to the table of contents.